MITRE ATT&CK v14 includes newly discovered sub-technique that will be used to bolster Wi-Fi Security on systems like Windows, MacOS, and Linux
Full Press Release: https://www.prnewswire.com/news-releases/cardinalops-contributes-to-mitre-attck-for-fourth-consecutive-release-301998990.html
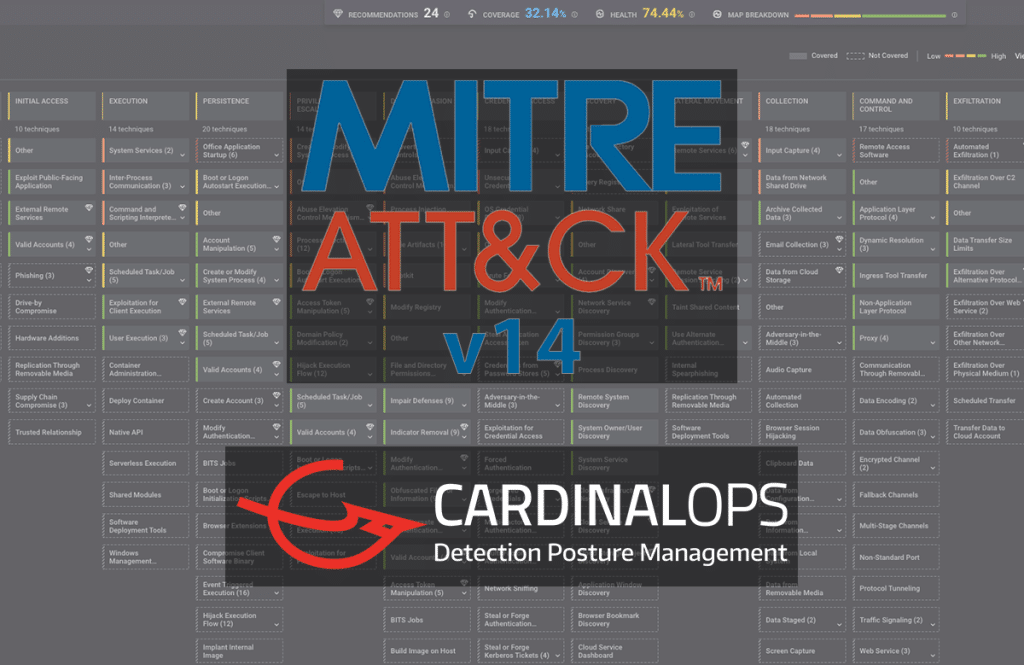
TEL-AVIV, Israel and BOSTON, Nov. 28, 2023 /PRNewswire/ — CardinalOps, the detection posture management company, announced today that it contributed updates to the latest version of MITRE ATT&CK, a globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. CardinalOps’ contributions to MITRE ATT&CK v14, which was released on Oct. 31, 2023, marks the fourth consecutive release of MITRE ATT&CK to which the CardinalOps team has contributed.
Containing over 800 techniques and sub-techniques employed by both cybercriminal and nation-state threat groups alike, MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is the industry-standard framework for understanding adversary playbooks and behavior. MITRE ATT&CK v14 introduced updates to techniques, groups, campaigns and software for Enterprise, Mobile, and ICS, including a large expansion of detection notes and analytics within techniques in Enterprise.
Liran Ravich, Cybersecurity Architect at CardinalOps, contributed a new sub-technique on Wi-Fi Discovery to the most recent version, as well as both a new technique and sub-technique specifically for Mobile, towards Defense Evasion (Data Destruction) and Impact (Masquerading) tactics, respectively.
Adversaries employ these methods by:
- Wi-Fi Discovery – Looking to Wi-Fi networks to access information from hosts. By targeting local Wi-Fi networks or networks to which a device has recently been connected, adversaries can access sensitive information like passwords and other personal data. MITRE ATT&CK v14 highlights how these discoveries are made on different systems, including Windows, MacOS, and Linux.
- Data Destruction – Disrupting the availability of systems, services, and network resources through the destruction of data and files in large numbers or on specific devices. This has the potential to render stored data irrecoverable by forensic techniques due to the overwriting of files or data on local and remote drives.
- Masquerading – Evading defenses and observation by matching or closely imitating names and locations of legitimate resources and files. This is achieved by assigning the same name or icon as a legitimate, trusted file or application to trick users into selecting the illegitimate version.
“CardinalOps is pleased to have the opportunity to collaborate with MITRE to contribute new techniques for the fourth consecutive release of ATT&CK,” said Yair Manor, CTO and co-founder of CardinalOps. “As the threat landscape continues to evolve and present greater cyber risks for organizations, it is important to continue to provide the defender community with resources that allow them to apply this knowledge and continue developing a strong detection posture.”
About CardinalOps
Backed by detection engineering experts with nation-state expertise, the CardinalOps platform uses automation and MITRE ATT&CK to continuously assess and improve the detection coverage of your existing SIEM and detection tools to enable a stronger, more resilient defense. What’s more, it improves detection engineering productivity by 10x and reduces the need to hire additional SOC personnel. Native API-driven integrations include Splunk, Microsoft Sentinel, IBM QRadar, Google Chronicle SIEM, CrowdStrike Falcon LogScale, and Sumo Logic. Learn more at cardinalops.com.